Why Ring Signatures Make Monero Feel Like Magic (and Where the Tradeoffs Lie)

Okay, so check this out—privacy tech rarely feels magical. Wow! Monero’s ring signatures do something close to that, though. They hide who sent what, and they make transaction history look like a crowded room where everyone is wearing identical coats. My gut said this was simple at first, but then the details tangled up and I had to slow down and actually think it through.
There’s a quick intuition: imagine mailing a letter from a stack of identical envelopes. Short. The observer can’t tell which envelope came from which person because they all look the same. Medium length explanation: ring signatures let a spender prove that one of a group of keys authorized a transaction without revealing which key did it, so the link between sender and output becomes ambiguous. Longer thought with some nuance: that ambiguity is probabilistic and cryptographically enforced, which means privacy isn’t about hiding facts but about creating strong uncertainty, and understanding the residual risks requires looking at protocol details, wallet practices, and network-level metadata.
Whoa! Seriously? Yeah. Initially I thought ring signatures were just one trick, but then I realized they’re part of a whole privacy dance—stealth addresses, confidential transactions, and now Bulletproofs for compact proofs—each step helps, and each step introduces tradeoffs. On one hand ring signatures blur sender attribution; on the other hand they make wallets more complex and transaction sizes larger (though compression improvements have reduced that pain). I’m biased, but this part bugs me: engineers must balance usability with cryptographic rigor, and sometimes the UX loses out.

How ring signatures actually work (without the math wall)
Here’s the thing. A ring signature mixes your real spend key with a set of decoy keys drawn from the blockchain. Short. The signature proves a member of that ring signed the transaction, but it doesn’t say which one. Medium explanation: cryptographically, the signer constructs a ring and generates a signature that is valid only if one of the private keys corresponding to the public keys in the ring was used; because of clever math, an outside verifier cannot pinpoint the actual signer. Longer thought: that construction relies on one-way functions and unlinkability properties so that the signature is simultaneously verifiable and anonymous, which is a subtle and powerful combination that moves privacy from “obscurity” to “provable uncertainty.”
Hmm… somethin’ else people often miss: the choice of decoys matters. Short. Decoys should look realistic. Medium: if a wallet picks decoys poorly—say, only very old outputs or very new ones—statistical analysis can weaken anonymity sets. Longer: wallet designers have worked hard on decoy selection algorithms to avoid awful patterns that would otherwise let observers correlate transactions with a higher-than-expected probability, and ongoing research keeps refining those heuristics.
I’ll be honest—there’s a myth floating around that ring signatures make Monero totally untraceable. Short. Not quite. Medium sentence: they make tracing far, far harder, shifting the burden to statistical attacks, heuristic weaknesses, and metadata like IP addresses. Long: when you combine imperfect client behavior (like reusing outputs in certain ways) with network-level leaks or poor peer-to-peer privacy, the mathematical obfuscation can be undercut, which is why holistic privacy practices are essential.
Hands-on privacy: wallets, behavior, and the network
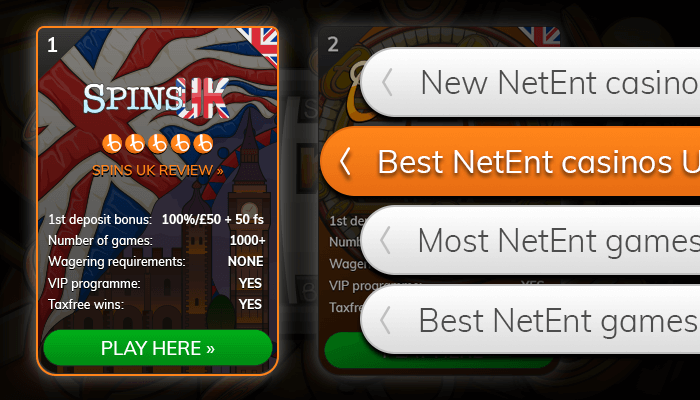
Okay, practical note: your choice of wallet matters. Short. Use a reputable, well-maintained wallet to minimize mistakes. Medium: for Monero that often means using the official GUI or trusted community wallets, and yes—if you’re getting started, check out a reputable option like the monero wallet to set up safely. Longer thought: wallets implement ring signature creation, decoy selection, and output handling, and a buggy or outdated wallet can leak info (timing, address reuse, user-set mixin choices in old versions), so the software layer is as important as the protocol layer.
Something felt off about early public discussions that treated privacy as just a protocol feature. Short. Real privacy is practice. Medium: protecting your transactions means considering how you connect to the network (use Tor/I2P or a trusted remote node), what devices you use, and how you manage seeds and backups. Longer: even with perfect cryptography, sloppy operational security—posting receipts online, reusing accounts linked to your identity, or running a wallet on an exposed machine—can reveal links that cryptography tries to obscure.
On the research side, ring signatures evolved. Short. Monero moved from simple ring signatures to ring confidential transactions (RingCT). Medium: RingCT combines ring signatures with confidential amounts so both the sender and the amounts can be hidden in a single construct. Longer sentence: this reduced the attack surface where amounts could be correlated across transactions, improving privacy but increasing validation complexity and CPU work, which then prompted optimizations like Bulletproofs to keep sizes and verification times reasonable.
At the community level there’s often tension between maximizing privacy and keeping the chain efficient. Short. People argue about block size, fees, and miner incentives. Medium: bigger transactions can mean higher fees or more storage cost long-term, so there’s real debate about what defaults should be. Long: some privacy features require mandatory adoption to be most effective (the more transactions that use the anonymity set, the better the cover), and persuading everyone—users, exchanges, service providers—to accept those defaults can be politically and economically tricky.
Threats, limits, and honest tradeoffs
Listen—no system is bulletproof. Short. Ring signatures dramatically raise the bar, but they don’t erase risk. Medium: if an adversary controls a large fraction of outputs or monitors network traffic, they can sometimes deanonymize users through correlative techniques. Longer: moreover, when law enforcement or attackers combine on-chain analysis with off-chain data (exchange KYC, IP logs, vendor receipts), they can often shrink the effective anonymity set in ways that cryptography alone can’t prevent.
Initially I thought technical fixes could close all gaps, but then I realized the social and infrastructural aspects are equally important. Short. On one hand, better protocol design helps. Medium: on the other hand, policy and user practices matter more than many enthusiasts admit. Long: so the most resilient approach blends strong cryptography, careful network hygiene, privacy-respecting service integration, and realistic expectations about what “untraceable” actually implies in mixed real-world threat models.
Here’s what bugs me about simple narratives: they promise total secrecy like a magic cloak. Short. That’s a dangerous narrative because it lulls people into risky behavior. Medium: a pragmatic privacy model says “reduce risk where you can, and be honest about residual vulnerabilities.” Longer: that means designing wallets that default to safe options, educating users, and pushing research that tightens gaps without making the system unusable or the costs prohibitive.
Frequently asked questions
Do ring signatures make Monero untraceable?
No—ring signatures greatly increase anonymity by hiding which output in a ring was spent, but they don’t create absolute secrecy. Short. They create strong cryptographic uncertainty. Medium: other vectors—network metadata, poor decoy selection, and off-chain linking—can reduce privacy. Longer: overall privacy depends on the entire ecosystem: wallet behavior, node connections, exchange policies, and how widely privacy features are adopted; so think holistically.
How many decoys should a transaction use?
Modern Monero enforces a default ring size (so you don’t choose manually). Short. That helps avoid user errors. Medium: larger rings improve anonymity sets but slightly increase transaction size and verification cost. Long: the community tends to favor mandatory minimums because privacy works best when everyone follows the same rules—uniformity avoids revealing who intentionally sought extra privacy or who skimped on protections.
What practical steps improve my Monero privacy?
Use updated wallets, avoid leaking metadata, and prefer privacy-respecting services. Short. Consider connecting over Tor or I2P. Medium: don’t reuse addresses in traceable systems, and be careful when moving funds through exchanges that require KYC if you want to maintain unlinkability. Longer thought: privacy is a chain of small decisions—each link matters—and combining good protocol-level privacy with good personal operational security is the only way to get reliably better outcomes.